Fix Route53 DNS Propagation Errors After Domain Transfer
Background
My friend recently had a strange DNS issue we couldn’t figure out. Once he transferred his domain from the existing registrar to AWS, DNS records were failing to resolve for some users. This resulted in email deliverabilty and website availability issues.
We verified that some DNS servers had no information about the domain via this DNS propagation checker. We also verified the issue by connecting to a few different VPN endpoints (e.g., from a European location) and seeing that the site was inaccessible.
After lots of Googling, we were stumped. Luckily, AWS Support helped us figure this out.
The Problem
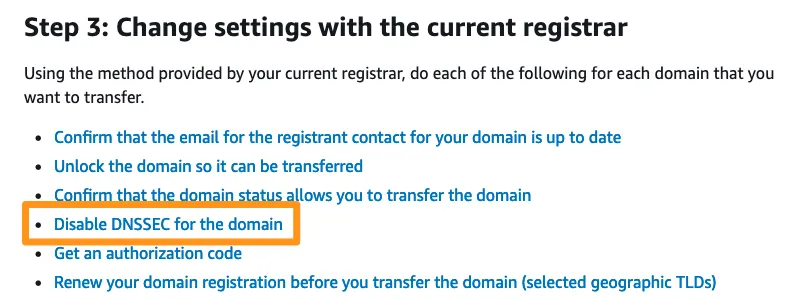
It turns out that a step was missed during the domain transfer process. From the Transferring registration for a domain to Amazon Route 53 documentation, Step #3 states that you must “Disable DNSSEC for the domain” before the transfer.
Because this step was missed, the DNSSEC settings transferred from the old registrar, but were not configured on the Route53 Hosted Zone. This mismatch caused non-authoritative DNS servers to fail to resolve the domain from AWS Name Servers.
Checking DNSSEC Settings
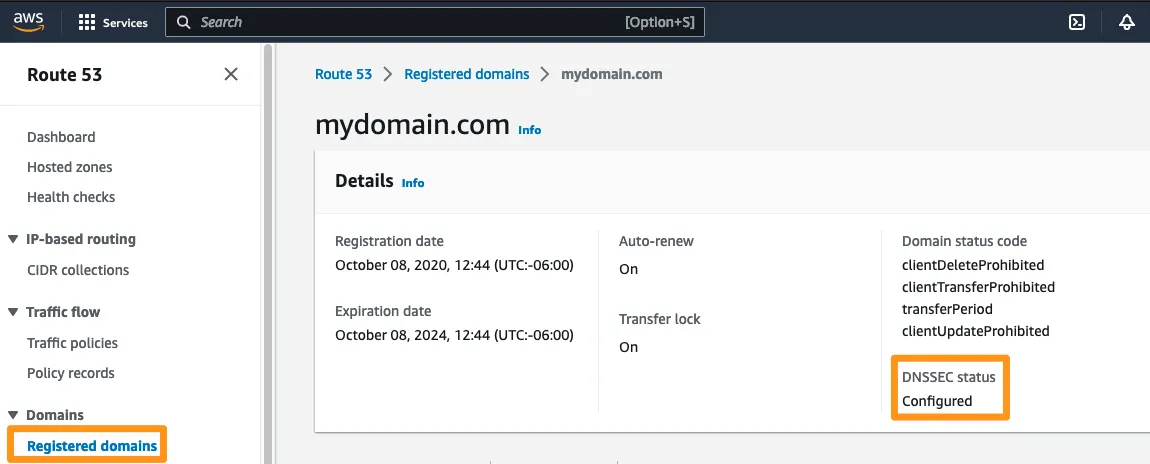
There are two places to look: on the registered domain and the hosted zone.
-
Check the DNSSEC settings on the registered domain in AWS Console. Once you choose you domain from the list, you’ll see a “DNSSEC Status” section. Note the current status (“Configured” or “Not Configured”).
-
Check the DNSSEC settings on the hosted zone in the AWS Console. Once you choose your domain’s hosted zone from the list, you’ll see a “DNSSEC signing” tab. Note the current status (“Signing” or “Not Signing”).
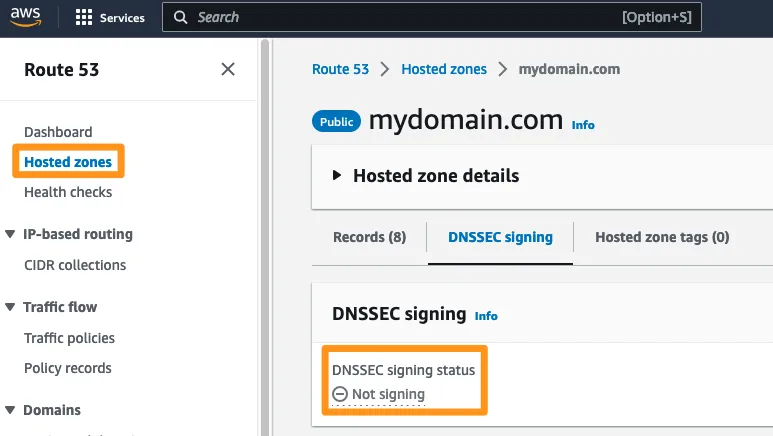
If, as in the screenshots, the domain is configured for DNSSEC, but the hosted zone is not, you’ll experience DNS problems with your domain.
Fixing the Problem
To fix the problem, match up the DNSSEC settings on the domain and the hosted zone. You can either disable DNSSEC on the registered domain or properly configure DNSSEC.
Either way, the settings need to match up between the domain and the hosted zone (enabled or disabled for both resources).
Conclusion
I’ll leave you with one of my favorite haiku: